Many businesses assume their IT systems are secure and efficient — until something goes wrong. Unexpected downtime, cyberattacks, or data loss often reveal hidden weaknesses that could have been prevented. That’s where IT Audits & Risk Assessment becomes essential.
A professional IT Audits & Risk Assessment helps businesses identify vulnerabilities, improve performance, and strengthen overall IT strategy. Instead of reacting to problems, businesses can take a proactive approach and prevent issues before they occur.
What Is an IT Audit & Risk Assessment?
IT Audits & Risk Assessment is a comprehensive evaluation of your entire IT environment, including:
- Network infrastructure
- Security systems
- Hardware and software
- Data protection processes
- User access and permissions
The goal of IT Audits & Risk Assessment is to identify risks, inefficiencies, and gaps in your system so they can be corrected before they lead to major problems.
Why IT Audits & Risk Assessment Is Important
Many IT issues develop quietly over time. Without regular evaluations, small problems can turn into serious risks.
A structured IT Audits & Risk Assessment helps businesses:
- Detect vulnerabilities before cyberattacks occur
- Improve system performance and reliability
- Ensure compliance with industry regulations
- Reduce downtime and unexpected failures
This proactive approach is a core part of effective Managed IT Support, helping businesses maintain stable and secure operations.
Key Areas Covered in an IT Audit
1. Network Security Evaluation
Your network is the foundation of your IT environment.
An audit reviews:
- Firewall configurations
- Access controls
- Network segmentation
A strong Network Security Setup ensures your systems are protected from unauthorized access and cyber threats.
2. Endpoint and Device Security
Every device connected to your network can be a potential entry point.
IT Audits & Risk Assessment evaluates:
- Antivirus and malware protection
- Device configurations
- Security updates
This works closely with Firewall & Endpoint Protection to ensure all devices are secure.
3. Data Protection and Backup Systems
Data is one of your most valuable assets.
An audit checks:
- Backup frequency and reliability
- Storage methods
- Recovery processes
A proper Data Backup & Disaster Recovery plan ensures your business can recover quickly from data loss.
4. System Performance and Infrastructure
Outdated or inefficient systems can slow down operations.
The audit evaluates:
- Server performance
- Network efficiency
- Hardware reliability
This connects directly with Server Setup & Maintenance to ensure your infrastructure supports your business needs.
5. Monitoring and Response Systems
Early detection is key to preventing major issues.
With 24/7 System Monitoring, businesses can:
- Detect unusual activity
- Respond to issues quickly
- Prevent system failures
Common Risks Identified During IT Audits
A thorough IT Audits & Risk Assessment often reveals:
- Weak passwords or poor access controls
- Outdated software and unpatched systems
- Misconfigured firewalls
- Lack of proper backups
- Inefficient network design
Identifying these risks early helps businesses avoid costly disruptions.
Benefits of IT Audits & Risk Assessment
1. Proactive Problem Prevention
Instead of reacting to issues, businesses can fix vulnerabilities before they cause damage.
2. Improved Security
Integrating findings with Network Security Setup and Firewall & Endpoint Protection strengthens overall protection.
3. Increased Efficiency
Optimizing systems improves performance and reduces downtime.
4. Better Decision-Making
Clear insights allow businesses to make informed IT investments and upgrades.
Best Practices for IT Audits & Risk Assessment
To maximize the value of your IT Audits & Risk Assessment:
- Conduct audits regularly (at least annually)
- Keep systems updated and patched
- Implement strong access control policies
- Monitor systems continuously
- Work with experienced IT professionals
These practices ensure your IT environment remains secure and efficient.
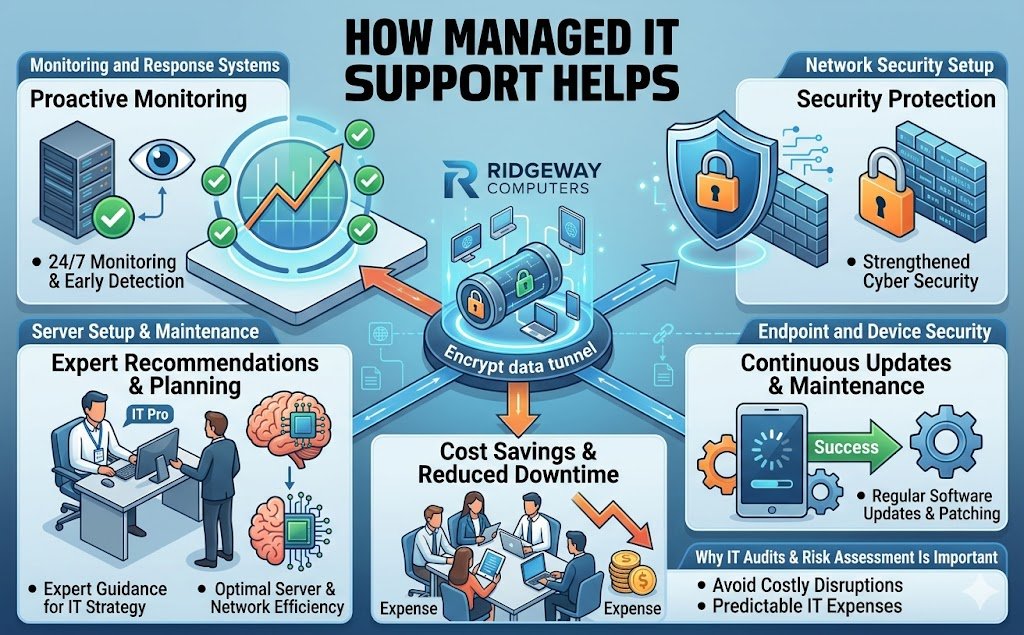
How Managed IT Support Helps
Managing IT audits internally can be complex and time-consuming. With Managed IT Support, businesses benefit from:
- Regular system evaluations
- Continuous monitoring and reporting
- Security updates and maintenance
- Expert recommendations and planning
For businesses in the GTA, Ridgeway Computers provides structured IT Audits & Risk Assessment services that help identify risks and improve long-term IT stability.
Conclusion
Hidden vulnerabilities can cause serious problems if left unchecked. IT Audits & Risk Assessment provides businesses with the insight needed to identify risks, improve performance, and strengthen security.
By combining:
- Network Security Setup
- Firewall & Endpoint Protection
- Data Backup & Disaster Recovery
- 24/7 System Monitoring
- Managed IT Support
Businesses can build a secure, reliable, and efficient IT environment.
Investing in IT Audits & Risk Assessment is not just about identifying problems — it’s about ensuring long-term success and stability.